SLAM: An Effective Method to Spot Even the Most Sophisticated Phishing Scams Targeting The Gullible
Cybercriminals are creating newer methods to phish gullible individuals every day. Opportunistic attackers are taking advantage of unaware employees and stakeholders to deploy phishing attacks in attempts to:
- Harvest credentials
- Install malware to businesses’ computers
- Steal money
With organizations having more remote employees now than ever, the risk has increased. You’ll see phishing scams everywhere — with cybercriminals posing as legitimate organization representatives to dupe employees and get access to businesses’ data and money.
Hackers also impersonate senior executives in companies and ask for credentials from unsuspecting employees.
Counter Attacking Phishing Attempts
The spike in phishing attempts emphasizes the need for training your employees to be extra diligent in identifying phishing scams. You need to help your employee develop a keen eye for phishing emails that could unleash a devastating ransomware attack that can cost your organization millions.
After all, phishing is the most common way attackers use to enter an organization’s system. The attackers rely on disguise and deception — turning a simple email into a highly disruptive attack. Fortunately, nearly all phishing attacks are preventable.
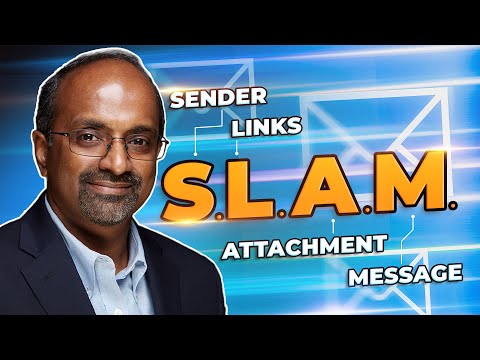
Using The SLAM Method to Identify Fraudulent Emails
Your organization can readily decrypt a phishing email using the SLAM method. SLAM is an acronym for what you should look for in an email to know if it’s a phishing attempt.
The term stands for the different parts of an email that everyone in your organization should check for before trusting it:
- S — Sender
- L — Links
- A — Attachment
- M — Message
Whenever you get an email from an unknown sender, you should critique the sender, link, attachment, and the message’s content to establish the email’s legitimacy.
Using the SLAM formula, you can build a strong cybersecurity culture and sharpen co-workers’ phishing detection skills.
Let’s examine how your organization should review these email areas.
Sender
Whenever your employees receive an email, they should carefully review the sender. You should learn to examine the sender past the name in the address bar because it might appear legitimate.
Your core target in the sender part should be the email address. Attackers often spoof email addresses, using domain names that aren’t legitimate. The cybercriminals will slightly misspell a domain to fool your eye. For instance, instead of cocacola.com, they can use cocacalo.com.
If you are in a rush when opening the email and glance at the sender’s address for milliseconds, you can easily miss the slight misspelling in the sender’s domain name.
You need a keen eye to examine the email address and ensure it’s accurate. If the email address is suspicious, you should conclude that it’s a phishing attempt and delete the email.
Links
The second part of the email you should examine is the links. Many phishers use links to deploy phishing attacks. The attacker will try to link your employee to malicious sites that can execute ransomware injections or steal credentials by spoofing a login page for a popular site.
What’s more concerning is that attackers can hide dangerous links behind images.
To overcome the deception, hover over any link in the email before clicking on them to check where they’ll take you. Hovering will reveal the real URL and should immediately reveal the phishing attempt, regardless of how convincing the message appears.
You should also visit the real sites that the hacker is trying to impersonate to confirm that the message is legit. For instance, don’t click the email link if you get an email from an attacker pretending to be Amazon claiming that your account has issues. Instead, open a browser and head to your Amazon site to check your account directly.
Attachments
Attackers can use all file attachments to hide malware — even innocent PDFs and Word Documents. Your employee should avoid opening file attachments they don’t know.
Even when the sender appears to be someone they know, they should consider if they were expecting the email or the attachment. If they weren’t expecting any email, they should execute the first step — reviewing the sender.
Your business should also invest in email filters and better antivirus or anti-malware applications. Email filters detect and block malicious codes in file attachments.
Message
The phishing world has become more sophisticated, and it’s hard to spot fake emails. However, some of the messages will still have slight mistakes when it comes to spelling and grammar.
Your best shot at identifying a phish from the message is by thoroughly scrutinizing the email. If anything from the message appears to be off, treat the email as a phishing attempt and don’t click on any link or download any attachment.
Another factor you can consider is the personalization of the email. If the sender mistypes the company name or your name, you should flag it as a potential phish.
Some phishers are aggressive and might spoof another company’s signature and logo. In such cases, check if the dates appear old. For instance, if the email has a copyright date in the signature and isn’t the current year, the email can be a scam.
The Basic Laws of Phishing That Criminals Use to Exploit The Human Part of An Organization
While the SLAM technique is excellent in identifying a phishing email, you should understand the core of the scam — every phishing attempt involves imitation.
Scammers will try to craft official-looking messages from another organization you have an account with. The email might have similar fonts, logos, and images to exploit the human part of your organization.
Your task in fighting phishing attacks is to decode through the social engineering techniques the attackers take to bait people to click malicious links, download infected attachments, or share credentials.
Veltec Networks Can Help Your Business Avoid Even The Most Sophisticated Phishing Attempt
Phishers are devising unique methods for phishing gullible co-workers in your organization. Their most recent attack strategy makes it nearly impossible to tell if an email is fake or genuine.
Without the proper knowledge, your organization remains under threat of constant social engineering and eventually hacked. As a result, Veltec Networks can help your organization readily identify and deal with phishing scams. Contact us today to help you stay safe in cyberspace.






